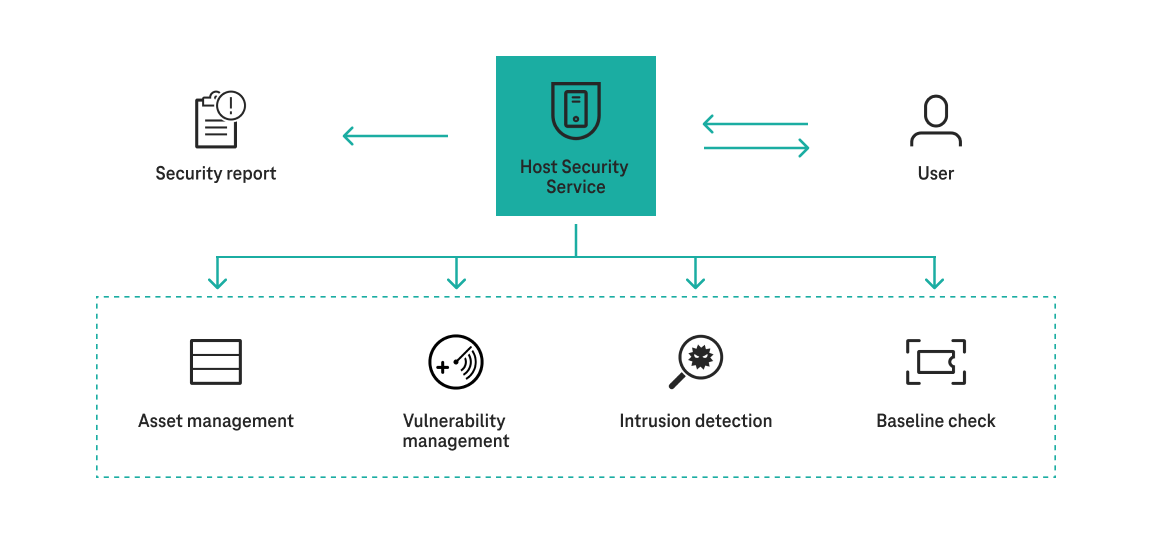
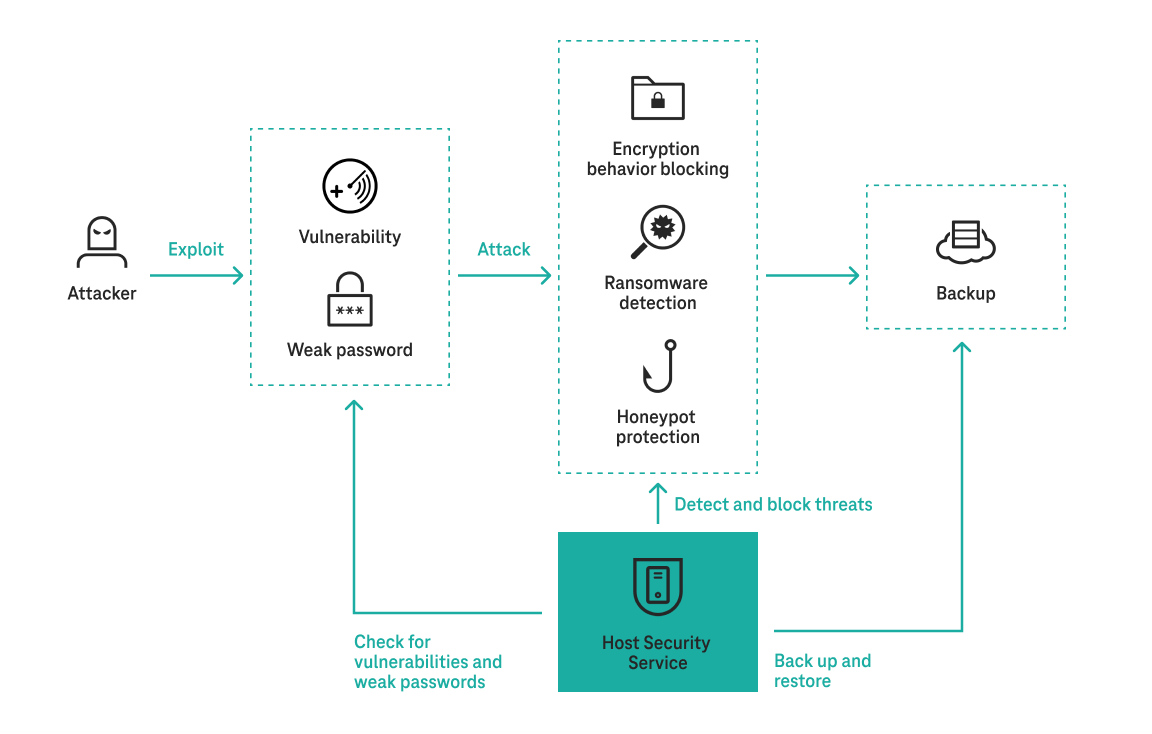
With Host Security Service (HSS), you can manage server and container risks and facilitate compliance with cybersecurity standards. Combat attacks such as ransomware, mining, infiltration and container escapes.
HSS is designed to protect server workloads in hybrid clouds and multi-cloud data centers. It provides host security features, container security features, and Web Tamper Protection (WTP).
The service can help you monitor and manage your servers and containers in a unified way, protect the integrity of your system, increase application security, monitor user operations, and detect intrusions.