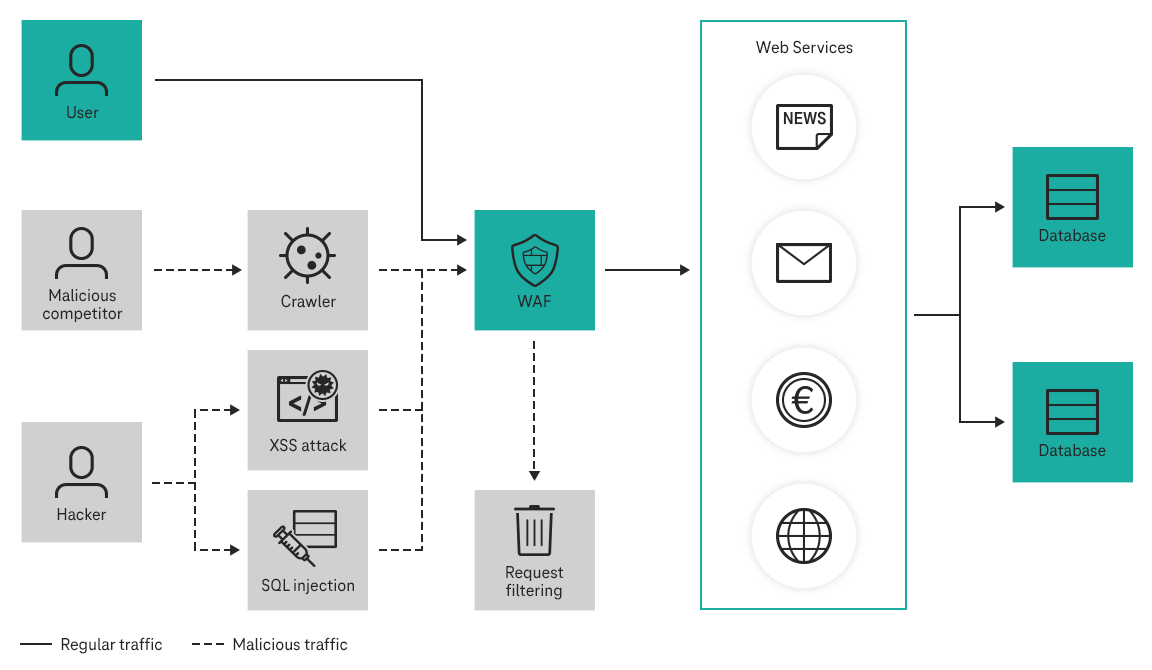
Because web applications can be attacked in a variety of ways, a range of different protection mechanisms need to be implemented. Alongside basic security mechanisms on network level and Anti-DDoS, the Open Telekom Cloud also offers a Web Application Firewall.
The Web Application Firewall (WAF) acts as a shield for web apps and websites against multiple attackers such as SQL injection, malicious file execution, cross-site scripting (XSS), and more to keep them stable and secure. The WAF analyzes incoming requests and the response of the corresponding server in the Open Telekom Cloud, intelligently filtering out malicious traffic to safeguard data, ensure fast load times, and maintain uptime.